The Zero Trust Stack Dilemma: Assemble or Consolidate?
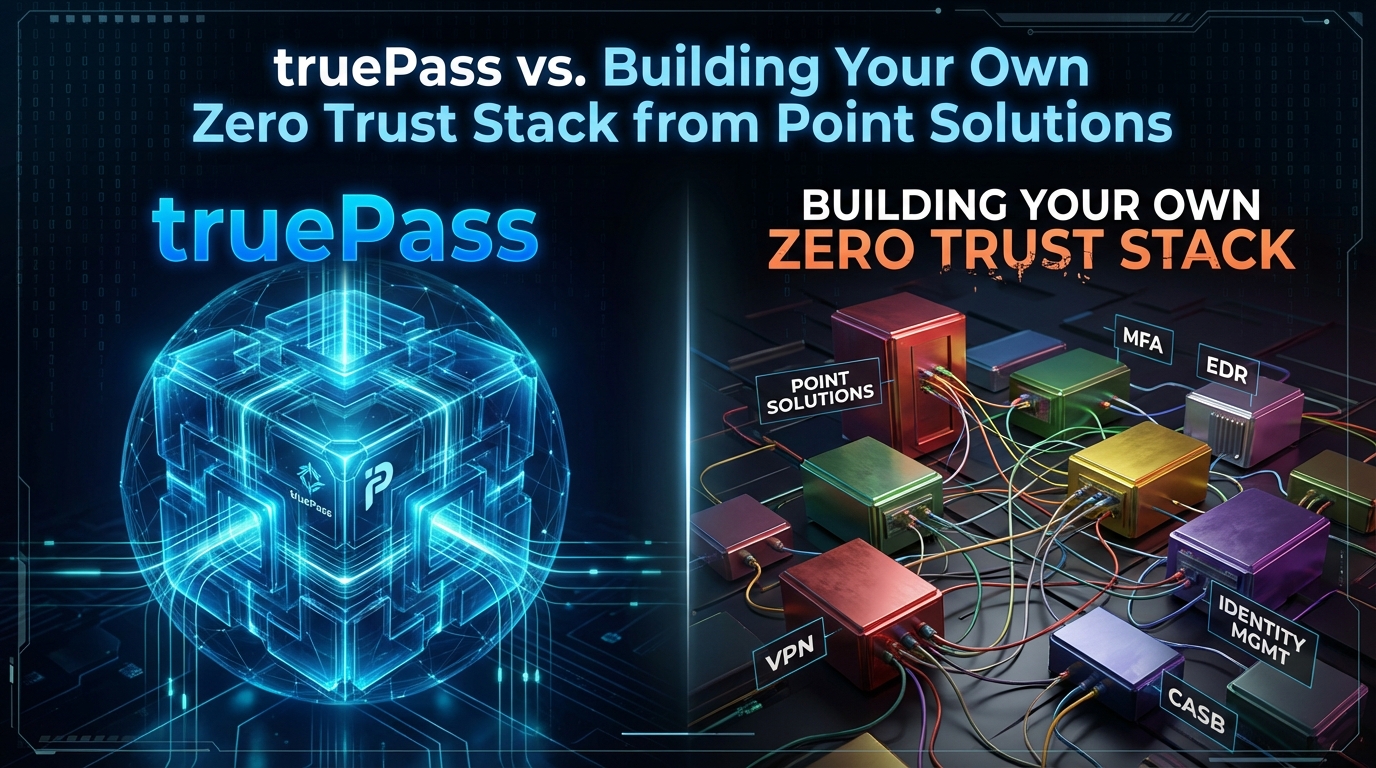
Every security team building a Zero Trust architecture faces the same strategic question: should you assemble best-of-breed point solutions from multiple vendors, or deploy a unified platform that combines ZTNA, microsegmentation, endpoint compliance, and identity-based access in a single product?
The question is not theoretical. According to Tailscale’s 2025 Zero Trust Adoption Survey, 92% of organizations use multiple tools for network security. Only 8% operate on a single unified platform. Nearly half – 48% – are actively trying to consolidate tools, but cite integration complexity, resource constraints, and vendor lock-in as barriers.
The cost of fragmentation is real. Organizations running point solutions report longer deployment timelines, higher operational overhead, policy inconsistencies across tools, and security gaps at the seams between products. Meanwhile, 88% of respondents reported at least one security incident in the past two years, including privilege misuse (24%) and security protocol bypass (22%).
This article provides a practical, technical comparison between building your own Zero Trust stack from point solutions and deploying a unified platform. It examines the true costs of each approach – not just licensing, but integration engineering, policy management, operational overhead, and security coverage gaps – and offers a decision framework for choosing the right path.
The Point Solution Approach: What You’re Actually Building
When organizations build Zero Trust from point solutions, they typically assemble components from four to six different vendors. A typical stack includes separate products for ZTNA, microsegmentation, MFA, endpoint protection, privileged access management, and SIEM integration.
Each product is selected for its strength in a specific capability. In theory, this delivers “best of breed” across every function. In practice, it creates an architecture that must be integrated, maintained, and coordinated across multiple vendor ecosystems – each with its own management console, policy engine, update cycle, API, and support channel.
The Typical Point Solution Zero Trust Stack
Zero Trust Function | Point Solution Category | Example Vendors | Typical Licensing Model |
Zero Trust Network Access | ZTNA-as-a-service | Zscaler ZPA, Cloudflare Access, Netskope | Per-user, per-month |
Microsegmentation | Network segmentation platform | Illumio, Guardicore (Akamai), ColorTokens | Per-workload or per-node |
Multi-Factor Authentication | Identity provider / MFA | Okta, Duo (Cisco), Azure AD | Per-user, per-month |
Endpoint Compliance | EDR / UEM | CrowdStrike, Microsoft Defender, SentinelOne | Per-endpoint, per-year |
Privileged Access Management | PAM platform | CyberArk, Delinea, BeyondTrust | Per-user or per-session |
Security Logging & Integration | SIEM / SOAR | Splunk, Microsoft Sentinel, QRadar | Per-GB ingested or per-event |
This means six vendor contracts, six management consoles, six API integrations, six support escalation paths, and six update cycles – all of which must work together to enforce a unified security posture.
The Five Hidden Costs of the Point Solution Approach
The licensing cost of point solutions is visible and well-understood. The hidden costs – which often exceed licensing by a factor of three or more – are where organizations underestimate the true investment.
1. Integration Engineering
Every point solution must integrate with every other point solution. ZTNA must receive device posture data from the endpoint protection tool. Microsegmentation must consume identity context from the IdP. PAM must feed session data to the SIEM. Each integration requires custom API work, data format mapping, and ongoing maintenance when either vendor releases an update that changes their API.
For a six-product stack, the number of potential integration pairs is 15 (n × (n-1) / 2). Each integration requires between 2 and 8 weeks of engineering effort for initial deployment, plus ongoing maintenance.
2. Policy Inconsistency
Each product has its own policy engine, its own policy language, and its own enforcement model. A conditional access policy defined in the IdP does not automatically propagate to the microsegmentation platform or the PAM tool. Security teams must manually replicate policy intent across multiple systems – and keep them synchronized when policies change.
This creates a real risk: a user may be blocked by the IdP but permitted by the ZTNA tool, or denied network access by microsegmentation but granted application access by the PAM solution. These inconsistencies are difficult to detect and can persist for weeks or months.
3. Operational Overhead
Each vendor console requires trained operators. Each product generates its own alerts, its own logs, and its own event format. Security analysts must context-switch between consoles, mentally correlate events from different systems, and investigate incidents that span multiple tools.
Gartner’s prediction that 70% of new remote access deployments will rely on ZTNA rather than VPNs reflects the direction of the market – but says nothing about the operational complexity of managing that ZTNA alongside five other point solutions.
4. Gaps at the Seams
The most dangerous vulnerabilities in a point solution architecture exist at the boundaries between products. Traffic that passes from the ZTNA tool to the internal network may not be inspected by the microsegmentation engine if the integration is misconfigured. Endpoint compliance checks may not trigger ZTNA policy revocation if the data pipeline between the two products is delayed.
Attackers exploit seams. They find the transitions where one tool hands off to another and target the gaps.
5. Vendor Dependency Risk
Each vendor in the stack represents a dependency. If one vendor is acquired, discontinues a product, or changes their API, the entire architecture is affected. The more vendors in the stack, the higher the probability that at least one will cause a disruption within any given year.
Hidden Cost Summary
Cost Category | Point Solutions (6 Vendors) | Unified Platform (1 Vendor) |
Licensing contracts | 6 separate contracts | 1 contract |
Management consoles | 6 consoles, 6 logins | 1 console |
Integration engineering | 15 potential integration pairs | Zero – native integration |
Policy engines | 6 separate policy languages | 1 unified policy engine |
Vendor support escalation | 6 separate support channels | 1 support channel |
Update coordination | 6 independent update cycles | 1 coordinated release cycle |
Staff training | Training across 6 products | Training on 1 platform |
Incident investigation | Cross-correlate 6 data sources manually | Single pane of glass |
Risk of vendor disruption | High (6× probability surface) | Low (1 vendor dependency) |
What a Unified Zero Trust Platform Actually Delivers
A unified Zero Trust platform combines multiple security functions – ZTNA, microsegmentation, MFA, endpoint compliance, and privileged access controls – in a single product with a single management interface, a single policy engine, and native integration between all components.
The value is not simply consolidation. It is the elimination of integration gaps, the enforcement of consistent policy across all functions, and the reduction of operational complexity from six parallel workflows to one.
The truePass platform is built on this principle. It integrates identity-based firewall (IDFW), microsegmentation, device compliance checking, endpoint security, and multi-factor authentication in a single deployment. Policies are defined once and enforced consistently across all functions – ZTNA, segmentation, and access control – without requiring separate integration work.
What Unification Means in Practice
When a unified platform processes an access request, every security function operates on the same data, at the same time, under the same policy. The device compliance check, identity verification, MFA challenge, segmentation policy evaluation, and access decision all happen within a single processing pipeline. There is no handoff between products, no API latency between vendors, and no risk of policy divergence.
For microsegmentation specifically, a unified platform applies identity-based segmentation policies that are tied directly to the user’s identity and device posture – not to static IP addresses or VLAN memberships. When the user moves between networks or devices, the segmentation policy follows them automatically.
This native integration is architecturally impossible in a point solution stack, where the segmentation engine and the identity provider are separate products from separate vendors, communicating through an API that introduces latency, failure modes, and synchronization risk.
Head-to-Head Comparison: Point Solutions vs. Unified Platform
The following table compares the two approaches across the dimensions that matter most to security teams evaluating their Zero Trust architecture.
Evaluation Criteria | Point Solutions Stack | Unified Platform |
Time to deploy basic ZT controls | Months (integration work required) | Weeks (native integration) |
Time to deploy advanced policies | Additional months per integration | Configuration within the same platform |
Policy consistency | Manual synchronization across tools; drift risk is high | Single policy engine; consistency enforced automatically |
Endpoint + network policy coordination | Requires API integration between EDR and segmentation | Native – endpoint posture directly informs segmentation |
MFA + access decision latency | Two products, two processing steps, API round-trip | Single processing pipeline, sub-second |
Microsegmentation granularity | Depends on segmentation vendor; may require separate agent | Identity-based, per-endpoint; same agent as ZTNA |
Agent count on endpoints | 3-5 agents (ZTNA, EDR, microseg, MFA, PAM) | 1 agent |
Vendor management overhead | 6 contracts, 6 support relationships, 6 renewal cycles | 1 contract, 1 support relationship |
Incident investigation | Correlate across 6 consoles manually or via SIEM | Single audit trail in one console |
Ongoing maintenance | Coordinate updates across 6 products; test compatibility | Single update cycle; vendor-tested compatibility |
Total cost of ownership (3-year) | Higher: licensing + integration + operational overhead | Lower: consolidated licensing, no integration cost |
Flexibility to swap components | High – can replace any individual product | Lower – platform-dependent |
The Integration Tax: Quantifying What You’re Actually Paying
Organizations rarely calculate the full cost of integration before committing to a point solution strategy. The following framework helps quantify the “integration tax” – the total cost beyond licensing that is required to make point solutions function as a cohesive Zero Trust architecture.
Integration engineering labor. Each vendor-to-vendor integration requires 2-8 weeks of security engineering time. At a fully-loaded cost of $150/hour for a senior security engineer, a single integration represents $12,000-$48,000 in labor. For a six-product stack with 15 integration pairs, the total initial integration cost ranges from $180,000 to $720,000.
Ongoing integration maintenance. Each vendor releases updates 4-12 times per year. Any update can break an existing integration. Assume 10% of updates require integration rework, at 1-2 weeks of engineering per fix. That represents 6-18 maintenance incidents per year across the stack.
Policy synchronization overhead. Security teams spend 5-10 hours per week ensuring policies are consistent across products. Over a year, this represents 260-520 hours of analyst time – the equivalent of 0.13-0.25 FTE dedicated solely to policy synchronization.
Agent conflicts and endpoint performance. Running 3-5 security agents on each endpoint creates resource contention, compatibility conflicts, and increased helpdesk tickets. Organizations report 15-30% higher endpoint-related support tickets when running more than three agents simultaneously.
These costs are invisible on a vendor’s quote but very real in the budget. A unified platform eliminates the integration tax entirely because all functions share a single codebase, a single agent, and a single policy engine.
When Point Solutions Still Make Sense
A unified platform is not the right answer for every organization. There are legitimate scenarios where point solutions remain the better choice.
You have an established, well-integrated stack. If your organization has already invested heavily in integrating best-of-breed tools and has mature automation connecting them, the cost of replacing a working architecture may exceed the cost of maintaining it. Evaluate the ongoing maintenance burden honestly before deciding.
You need a specific capability that no unified platform provides. Some specialized functions – deep cloud workload protection, niche protocol support, or highly specific regulatory tooling – may only be available from specialized vendors. In these cases, supplementing a unified platform with targeted point solutions is a pragmatic approach.
Your organization mandates multi-vendor diversity. Some regulatory frameworks or internal policies require that no single vendor controls the entire security stack. In these environments, point solutions are a compliance requirement, not a choice.
You are early in your Zero Trust journey. If you are deploying one function at a time – starting with MFA, then adding ZTNA – a phased approach with individual products can reduce upfront risk. However, plan for consolidation early. Adding products without a consolidation strategy guarantees integration debt.
For most enterprise organizations, however, the integration tax and operational overhead of point solutions outweigh the theoretical benefits of best-of-breed selection. The 92% of organizations currently running multiple tools – and the 48% actively trying to consolidate – reflect this reality.
How truePass Addresses the Unified Platform Requirement
truePass was designed from the ground up as a unified Zero Trust security platform, not a collection of acquired products bolted together. It combines five core functions in a single deployment.
Identity-Based Firewall (IDFW). Firewall protection is embedded directly at the endpoint level. Access decisions are based on the user’s verified identity, not on network location or IP address. This eliminates the need for a separate network firewall product for east-west traffic control.
Microsegmentation. Each endpoint operates as its own security zone. Segmentation policies follow the user’s identity and device posture. Even if one endpoint is compromised, the breach cannot propagate to other segments. There is no separate microsegmentation product to integrate – it is a native function of the platform.
Device and System Compliance Checks. truePass continuously evaluates device posture – firewall status, OS patch level, running processes, and geolocation. Non-compliant devices are blocked before they connect, not after. This replaces the need for a separate UEM or endpoint compliance tool.
Multi-Factor Authentication. The platform includes native MFA supporting FIDO2, hardware keys, WhatsApp, Telegram, Duo, and Okta integration. MFA is enforced as part of the access decision pipeline – not as a separate product that feeds data into the ZTNA tool through an API.
Zero Trust network access using patented Reverse Access technology. No inbound connections are required. Applications are completely hidden from unauthorized users. Access is granted at the application layer, not the network layer, and the connection is temporary – automatically terminated when the session ends.
Because these functions share a single agent, a single policy engine, and a single management console, truePass eliminates the integration tax that makes point solution stacks expensive and fragile. A policy change propagates instantly across ZTNA, segmentation, and endpoint compliance – because they are not separate products.
Organizations operating in environments with complex regulatory requirements – from capital markets and insurance to retail operations – benefit particularly from unified policy enforcement, where a single platform ensures that access controls, segmentation, and compliance requirements are applied consistently without the synchronization risk that multi-vendor architectures introduce.
Decision Framework: Choosing Between Unified and Point Solution
Use this framework to evaluate which approach fits your organization.
Choose a Unified Platform When:
- You are deploying Zero Trust for the first time and want the fastest path to coverage
- You are currently running 4+ security tools and experiencing integration fatigue
- Your security team has fewer than 10 people and cannot support multi-vendor operations
- You need consistent policy enforcement across ZTNA, segmentation, and endpoint compliance
- You want to reduce agent count on endpoints from 3-5 to 1
- Your primary goal is rapid deployment with predictable ongoing costs
- You need a single audit trail for compliance reporting
Choose Point Solutions When:
- You have a mature, automated integration layer connecting your existing tools
- You require a specific niche capability not available in any unified platform
- Regulatory requirements mandate multi-vendor diversity
- You have a dedicated integration engineering team with capacity to maintain vendor-to-vendor connections
- You are deploying a single Zero Trust function as a pilot before committing to a full architecture
Key Questions to Ask Before Deciding
Question | If Yes → Consider | If No → Consider |
Do we have engineering staff to maintain 15+ integrations? | Point solutions if you have capacity | Unified platform |
Are we experiencing policy drift between our existing tools? | Unified platform to eliminate drift | Point solutions may be working |
Do our endpoint agents conflict with each other? | Unified platform (single agent) | Current stack may be stable |
Can we deploy full Zero Trust in under 90 days? | Current approach may be adequate | Unified platform for speed |
Do we have a single audit trail for compliance? | Current tools may suffice | Unified platform for auditability |
Are we paying more for integration than for licensing? | Unified platform to cut integration tax | Point solutions may be cost-effective |
Conclusion: The Architecture Decision That Shapes Everything After It
The choice between a unified Zero Trust platform and a point solution stack is not a product decision – it is an architecture decision that determines your operational overhead, your security coverage gaps, and your ability to enforce consistent policy across your entire environment for years to come.
Point solutions deliver theoretical best-of-breed capability at the cost of real-world integration complexity. The 92% of organizations running multiple tools – and the 48% trying to consolidate – demonstrate that the industry has learned this lesson through experience.
A unified platform like truePass eliminates the integration tax, reduces agent count, enforces consistent policy from a single engine, and provides a single audit trail. It trades the flexibility of swapping individual components for the certainty that all Zero Trust functions work together natively, without gaps at the seams.
For most organizations, the practical question is not whether to consolidate, but when. The earlier you make the architecture decision, the less integration debt you accumulate – and the faster you achieve the security posture that Zero Trust promises.