The Uncomfortable Question Your Board Will Eventually Ask
Your organization spent significant capital on data diodes. The hardware works. The unidirectional guarantee is physically enforced. No one disputes the security properties of a device that converts data to light and removes the return path at the photonic level.
But your board will eventually ask a different question: Why do we have four separate products managing connectivity between IT and OT, and why are our operational teams still requesting workarounds for every use case the diode cannot handle?
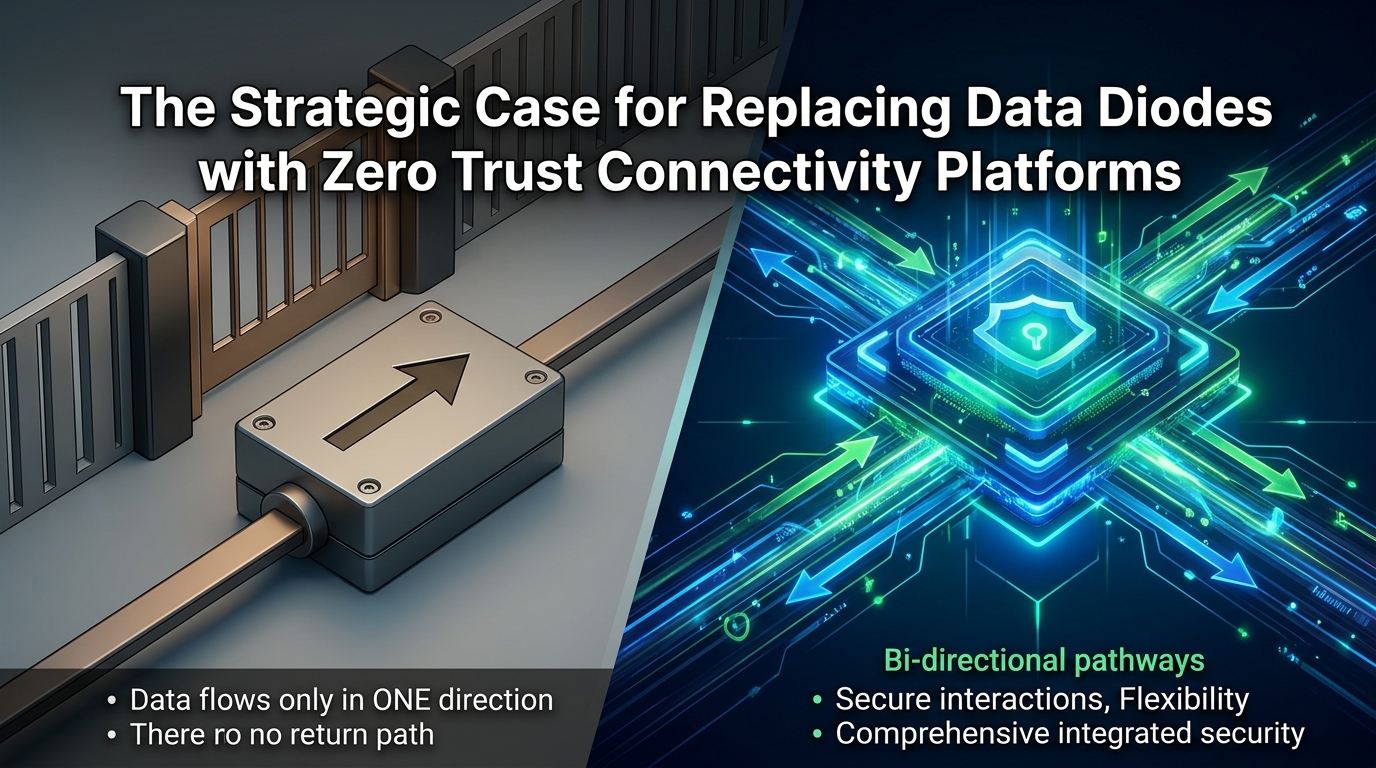
This is the question that exposes the gap between what data diodes were designed to do and what modern OT environments actually require. The diode handles unidirectional file transfer and data replication – historian mirroring, log export, SCADA telemetry to enterprise analytics. It does this with hardware-enforced certainty that no software-based solution can match. That is not in dispute.
What is in dispute is whether unidirectional file transfer covers the full connectivity requirement. In 2026, for most organizations operating in energy, water, manufacturing, defense, and critical infrastructure, it does not. The operational reality includes interactive application access (RDP to SCADA workstations, SSH to engineering servers, HTTP to internal web applications), controlled file sharing between environments (firmware updates, configuration backups, vendor deliverables via SMB), and machine-to-machine API connectivity (real-time sensor synchronization, cross-zone Web Services, IT/OT integration platforms). None of these work through a unidirectional device. Physics prevents it.
The result is what the industry calls “patchwork architecture” – and what your CFO calls “unplanned spend.” A data diode for one-way transfers. A separate SMB proxy for file sharing. A point TCP connector for one specific application. A VPN with a jump server for vendor RDP access. Each solution from a different vendor, with its own console, its own log format, its own maintenance cycle, and its own attack surface. The Waterfall Threat Report 2026 documented 57 cyber attacks causing physical consequences in heavy industry in 2025. Dragos reported that ransomware affiliates consistently exploited VPN portals and remote access tools – the exact supplementary products organizations deploy because their diode cannot handle interactive sessions.
This article provides the strategic framework for evaluating whether to replace data diode zero trust platform architectures that consolidate all three connectivity types – files, applications, and segmented network access – into a single platform with zero inbound ports. It is written for the CISO building a board-level business case, not for the engineer configuring the solution.
What Data Diodes Actually Protect – and Where They Stop
A data diode provides one security property with absolute certainty: no data can travel from the receiving network back to the sending network. This is enforced by physics – the optical transmitter on the sending side has no corresponding receiver, so there is literally no physical path for return traffic.
This property is valuable in specific scenarios. ISA/IEC 62443-3-3 specifies that achieving Security Level 4 (protection against state-sponsored attackers with sophisticated capabilities) requires “logical and physical isolation of critical networks.” Data diodes satisfy the physical isolation requirement in a way that firewalls and software-based solutions cannot. NIST SP 800-82 Rev. 3 recommends data diodes as part of OT network architecture for outbound data transfer. The US Nuclear Regulatory Commission’s RG 5.71 mandates one-way data flow from the highest security level systems to lower levels, implemented in hardware.
These are real requirements with real regulatory weight. Any replacement strategy must account for them.
But data diodes have inherent limitations that are structural, not fixable through product improvement:
TCP protocol incompatibility. Data diodes physically break TCP/IP because the protocol requires acknowledgments (ACKs) from the receiver back to the sender. Since no return path exists, standard TCP-based applications cannot function. Waterfall Security themselves acknowledge that data diodes “are constrained to connectionless protocols such as broadcast Ethernet and broadcast UDP/IP systems,” making integration into conventional networks difficult. Unidirectional gateways add software to replicate servers on the receiving side, enabling enterprise users to interact with copies of OT data – but the OT-side applications themselves remain inaccessible.
No interactive application access. When an OT engineer needs to RDP into a SCADA workstation for diagnostics, or a vendor needs SSH access to a PLC engineering station for firmware updates, or an operator needs to reach an internal web application – the diode cannot help. These are bidirectional sessions by nature. The diode was never designed for them. It is not a limitation to be patched; it is the fundamental architecture.
No identity awareness. A data diode transfers bits. It does not know who initiated the transfer, what device they are using, whether they passed multi-factor authentication, or whether their access should be time-bounded and recorded. The security property is directional enforcement, not identity-based access control. In a Zero Trust model – where every access request must be authenticated, authorized, and continuously validated – the diode addresses only one dimension of the problem.
Per-protocol deployment model. Each data type typically requires its own diode configuration or separate gateway software module. Historian replication needs one configuration. OPC-DA mirroring needs another. File transfer needs a third. Syslog forwarding needs a fourth. This creates deployment complexity and cost that scales with the number of data types, not the number of security policies.
The Hidden Cost: What Grows Around the Diode
The diode itself is not the cost problem. The cost problem is everything else the organization deploys to handle the connectivity the diode cannot provide.
A typical critical infrastructure organization with data diodes in production also operates:
A VPN concentrator in the IDMZ – for vendor and employee remote access to OT systems. This is the single most exploited attack vector in OT environments. Claroty’s 2026 analysis found that 82% of verified OT intrusions used internet-facing remote access tools as the initial entry point. The VPN exists because the diode cannot provide interactive application access like RDP to SCADA systems.
A jump server – for RDP access to SCADA workstations, historian servers, and engineering stations. The jump server has network-level access to the SCADA zone, creating a lateral movement pathway that defeats the segmentation the diode was supposed to enforce.
An SMB proxy or file gateway – for bidirectional file sharing between IT and OT environments. Firmware updates, configuration backups, vendor deliverables, and engineering documents all require controlled bidirectional transfer that the diode cannot support.
Point TCP connectors – for specific applications that require bidirectional communication. These are often embedded in vendor products, poorly documented, inconsistently managed, and invisible to the security operations center.
Each of these supplementary products has its own vendor, its own update cycle, its own log format, and its own attack surface. The CISO’s operational reality is not “we have a data diode protecting OT.” It is “we have a data diode plus four other products, and the four other products are where the attacks come in.”
The TCO calculation the board needs to see:
Cost Category | Data Diode + Supplements | Consolidated Platform |
Hardware (diode appliance) | $80K–$250K per site | Not applicable (VM-based) |
VPN concentrator + licensing | $15K–$40K per site | Eliminated |
Jump server infrastructure | $10K–$25K per site | Eliminated |
SMB proxy / file gateway | $20K–$50K per site | Included in platform |
Point TCP connectors | $5K–$15K per application | Included in platform |
Annual maintenance (all products) | $30K–$80K per site | Single contract |
Integration labor (4+ consoles) | 0.5–1 FTE | Single console |
SIEM integration (4+ log formats) | 40–80 hours initial + ongoing | Single Syslog feed |
Incident response complexity | 4+ vendor escalation paths | Single vendor |
Vendor count | 4–6 | 1 |
The hardware diode is the most expensive single item, but the supplementary products collectively cost more – and they are where the security risk concentrates.
The Architectural Alternative: Zero Inbound Ports Without Unidirectionality
The core insight behind replacing a data diode with a zero trust connectivity platform is this: the security property the CISO actually needs is not unidirectional data flow. It is zero inbound attack surface.
A data diode achieves zero inbound attack surface by removing the physical return path. That works – but it also removes the ability to do anything bidirectional.
A reverse-access architecture achieves zero inbound attack surface differently: the component inside the OT network initiates all connections outbound (HTTPS 443, TLS 1.2/1.3) to a gateway in the DMZ. The firewall remains in permanent deny-all for inbound traffic. No ports open inward. No services listen on the OT side. No IP addresses are discoverable from the outside. From the attacker’s perspective, the result is identical to a diode: there is nothing to scan, nothing to probe, nothing to exploit.
From the organization’s perspective, the result is fundamentally different: the outbound tunnel supports bidirectional application sessions – RDP, SSH, HTTP – because the protocol runs inside an already-established outbound connection. The three-layer approach to securing IT-to-OT connectivity combines reverse-access infrastructure (Layer 1), controlled file sharing with CDR scanning (Layer 2), and zero trust application access with per-session MFA and recording (Layer 3) into a single platform with unified policy enforcement.
Security comparison – what the board needs to understand:
Security Property | Data Diode | Zero Trust Connectivity Platform |
Inbound ports on OT firewall | Zero (physical) | Zero (architectural) |
Discoverable services on OT network | None | None |
Return path from receiving to sending network | Physically impossible | Architecturally prevented (outbound-only connections) |
Bypass via software vulnerability | Impossible (hardware-enforced) | Possible in theory (software-based) – mitigated by continuous patching + defense-in-depth |
Interactive application access | Not supported | Supported with per-session MFA, recording, and policy enforcement |
Identity-based access control | Not applicable | Full Zero Trust: identity, device posture, time window, approval workflow |
Session recording and audit trail | Not applicable | Built-in: video, keystroke, screen capture per session |
Compliance with IEC 62443 SL4 physical isolation | Yes – hardware-enforced | Partial – logical isolation, not physical. Requires risk acceptance or compensating controls |
NIST SP 800-82 Rev. 3 alignment | Full for outbound data transfer | Full for segmentation, access control, and monitoring; partial for unidirectional requirement |
The honest assessment: a zero trust connectivity platform does not provide the physical impossibility guarantee of a hardware diode. It provides an architectural guarantee – enforced by software configuration, not by photonics. For environments where regulation mandates physical unidirectional enforcement (nuclear facilities under RG 5.71, certain defense classifications), the diode remains necessary for that specific data flow. For the remaining 70–80% of IT/OT connectivity – interactive sessions, bidirectional file sharing, API integration, vendor access – the platform covers what the diode structurally cannot.
The Board-Level Business Case: Five Arguments
Argument 1: Attack Surface Reduction Through Consolidation
The data diode protects one connectivity type. The four supplementary products each introduce their own attack surface. Consolidating all connectivity into a single platform with zero inbound ports eliminates the VPN concentrator (the most exploited component), the jump server (the lateral movement enabler), and the point connectors (the unmanaged gaps). The net attack surface after consolidation is smaller than the current state, even though the platform is software-based rather than hardware-enforced.
Present this as: “We are replacing five attack surfaces with one – and the one has zero inbound ports.”
Argument 2: Operational Efficiency and Vendor Consolidation
Four to six vendors means four to six contracts, four to six renewal cycles, four to six escalation paths during an incident, and four to six log formats that the SOC must normalize. truePass Gravity consolidates file transfer (SMB Proxy with CDR), application access (RDP, SSH, HTTP with MFA and session recording), and reverse-access infrastructure into one platform, one console, one audit trail, and one Syslog feed to the SIEM.
Present this as: “We reduce vendor count from five to one, eliminate integration labor, and give the SOC a single source of truth for all IT/OT connectivity.”
Argument 3: Incident Response Speed
When a security event occurs at the IT/OT boundary, the IR team currently must correlate logs from the diode’s management interface, the VPN concentrator, the jump server’s Windows Event Logs, the SMB proxy, and whatever point connectors are deployed. Different time formats, different identifiers, different levels of detail. A consolidated platform provides a single chronological record per session: who authenticated, from which device, at what time, to which specific OT resource, with what policy authorization, and a full recording of every action taken during the session. Mean time to investigate drops from hours to minutes.
Present this as: “One log, one timeline, one recording per session. The IR team can answer ‘who did what, when, and to which SCADA workstation’ in under five minutes.”
Argument 4: Zero Trust Compliance Trajectory
Every major regulatory framework is moving toward Zero Trust. The DoD issued DTM 25-003 in July 2025, directing all components to achieve target-level Zero Trust across all systems including OT. The January 2026 Five Eyes guidance (CISA, NCSC-UK, BSI, FBI, and others) established secure connectivity principles for OT that emphasize identity-based access, continuous authentication, and granular policy enforcement – none of which a data diode provides. NIST SP 800-207 (Zero Trust Architecture) requires per-request access decisions based on identity, device health, and behavioral context.
A data diode satisfies the physical segmentation requirement but provides no identity, no authentication, no authorization, and no behavioral monitoring. The supplementary products may provide some of these individually, but without integration they cannot deliver the continuous, per-request access decisions that Zero Trust mandates. A consolidated platform that combines reverse-access, identity-based policy, per-session MFA, device posture verification, and unified audit inherently satisfies Zero Trust requirements across all connectivity types.
Present this as: “The regulatory trajectory is toward Zero Trust, not toward more diodes. We need to get ahead of the compliance curve, not behind it.”
Argument 5: Scalability and Multi-Site Deployment
Data diode hardware scales per-site and per-data-type. Each new site requires physical appliances ($80K–$250K), installation, configuration, and ongoing maintenance. Each new data type or application may require additional gateway software modules. A software-based platform deploys on standard VMs, configures through a central console, and scales by adding users and policies – not by adding hardware. For organizations with 10, 50, or 200 OT sites, the deployment and operational cost difference is substantial.
Present this as: “We can deploy secure connectivity to a new site in days, not months – and without a hardware procurement cycle.”
The Migration Path: Parallel Operation, Not Rip-and-Replace
No CISO should propose removing data diodes overnight. The migration is phased, with the diode and the platform running in parallel until the platform has demonstrated equivalent or superior security coverage for each connectivity type.
Phase 1: Deploy the Platform for Interactive Access (Months 1–3)
Replace the VPN concentrator and jump server with the zero trust connectivity platform. This addresses the highest-risk components first – the internet-facing VPN and the lateral-movement-enabling jump server – while the diode continues handling unidirectional data flows unchanged.
Success criteria: All RDP, SSH, and HTTP sessions to OT resources route through the platform with per-session MFA, session recording, and per-workstation policies. VPN concentrator decommissioned. Jump server decommissioned. External scan confirms zero discoverable services.
Phase 2: Migrate File Sharing to the Platform (Months 3–6)
Move bidirectional file sharing (firmware updates, configuration backups, vendor deliverables) from the standalone SMB proxy to the platform’s integrated SMB Proxy with CDR scanning. The diode continues handling one-way data replication (historian, syslog) during this phase.
Success criteria: All bidirectional file transfers route through the platform with Kerberos/NTLM authentication, SMB Signing, encryption, and CDR scanning. Standalone SMB proxy decommissioned.
Phase 3: Evaluate Diode Replacement for One-Way Flows (Months 6–12)
For each one-way data flow currently handled by the diode, evaluate whether the platform’s reverse-access architecture provides acceptable security. For historian replication and syslog forwarding – where the requirement is outbound data transfer, not physical unidirectionality – the platform’s outbound-only architecture typically provides equivalent protection with the added benefit of identity-based access control and unified audit.
Decision criteria per flow:
Flow Type | Regulatory Requirement | Replace Diode? |
Historian replication to enterprise | No physical isolation mandate | Yes – platform provides outbound-only transfer with identity, audit |
Syslog forwarding to SIEM | No physical isolation mandate | Yes – platform provides outbound-only Syslog with unified audit |
SCADA telemetry to analytics | Depends on sector regulation | Evaluate per regulation |
Nuclear safety data (RG 5.71) | Physical unidirectional mandate | No – retain diode for this specific flow |
Defense classified data (SL4) | Physical isolation mandate | No – retain diode for this specific flow |
Phase 4: Steady State
The typical end state is: platform handles 80–90% of IT/OT connectivity (interactive sessions, file sharing, most data transfers). Diode retained for 10–20% of flows where physical unidirectional enforcement is mandated by regulation. The patchwork of VPN, jump server, SMB proxy, and point connectors is fully eliminated.
What This Is Not: An Argument That Diodes Are Bad
Data diodes are excellent at what they do. The physics-based security guarantee is real and valuable. No software vulnerability can bypass a device that has no return optical path. For nuclear facilities operating under RG 5.71, for defense installations requiring IEC 62443 SL4 physical isolation, and for any environment where regulation explicitly mandates hardware-enforced unidirectional data flow – the diode is not optional. It is a compliance requirement.
The argument is not “diodes are bad.” The argument is “diodes alone are insufficient.” The moment an organization needs interactive application access, bidirectional file sharing, or machine-to-machine API connectivity across the IT/OT boundary – and virtually every organization does – the diode cannot help, and the supplementary products that fill the gap create more risk than the diode eliminates.
The strategic question for the CISO is not whether to use diodes or platforms. It is whether to continue expanding a patchwork of point products around a diode, or to consolidate the majority of connectivity onto a single platform that achieves the same zero-inbound-port security outcome – and retain the diode only where regulation demands physical unidirectionality.
Conclusion
The data diode was the right answer to a simpler question: how do we move data out of OT without allowing anything back in? The question has changed. Organizations now need full connectivity – files, applications, APIs – between IT and OT, with zero inbound attack surface, identity-based access control, per-session audit, and compliance with Zero Trust mandates that did not exist when the diode was deployed.
To replace data diode zero trust platform architectures, CISOs do not need to abandon the security principles that diodes represent. They need to extend those principles – zero inbound ports, invisible infrastructure, deny-all by default – to connectivity types that diodes were never designed to handle. The platform does not weaken the security posture. It eliminates the supplementary products that do.
The board presentation is three slides: Slide one – the current state (diode + 4 products, 5 vendors, 5 attack surfaces, fragmented logs). Slide two – the target state (platform + diode only where mandated, 1–2 vendors, 1 attack surface with zero inbound ports, unified audit). Slide three – the migration path (parallel operation, phased cutover, measurable success criteria at each phase).
The diode stays where regulation demands it. Everything else consolidates. The attack surface shrinks. The SOC gets one log. The board gets one vendor. And your OT engineers get full connectivity to the systems they need – without a single inbound port.