The Lateral Movement Problem in OT Networks
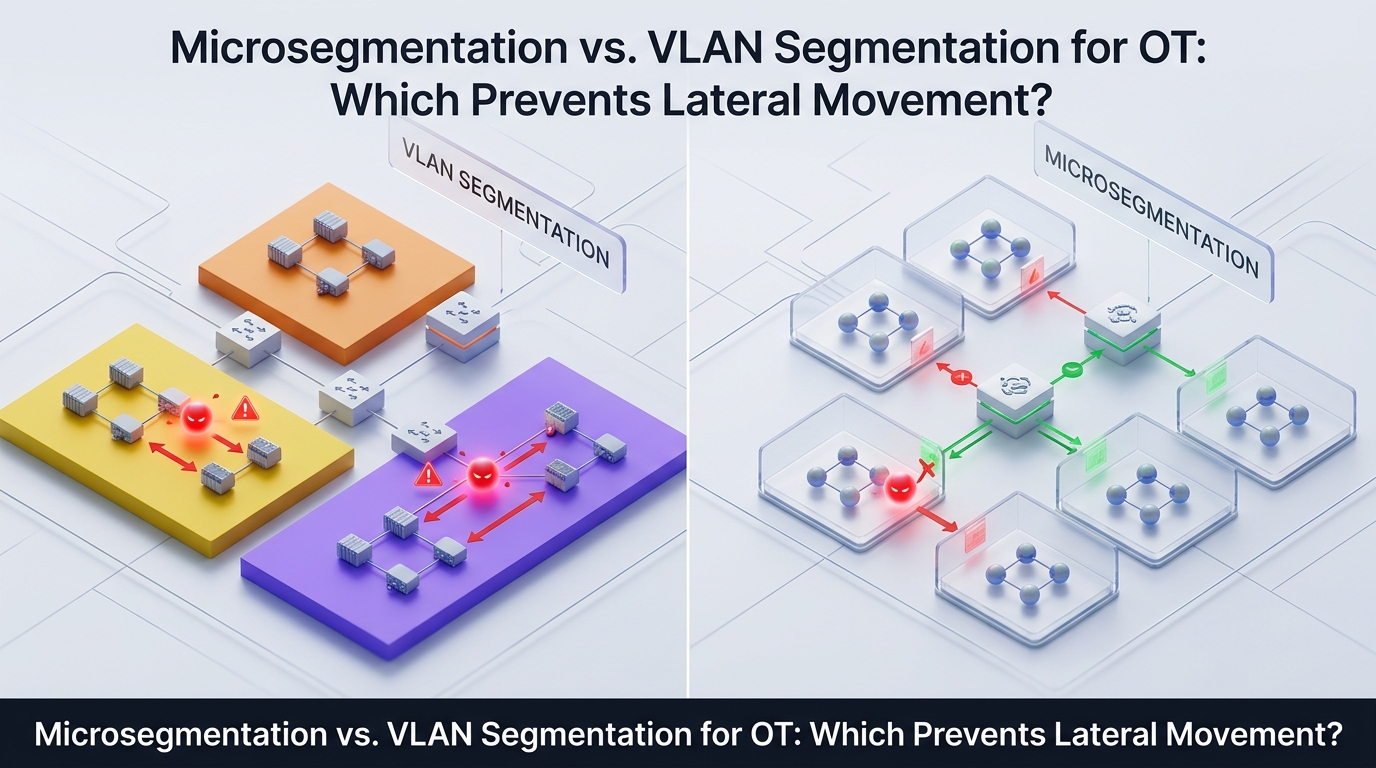
Ransomware attacks against industrial organizations increased 87% year-over-year in 2024, making OT the top ransomware target for four consecutive years. Dragos tracked 119 ransomware groups targeting industrial organizations in 2025 – a 64% increase from 2024. In nearly every case, the attack pattern was the same: gain initial access through an IT vector (VPN credentials, phishing, vulnerable web application), then move laterally until reaching OT systems that control physical processes.
Claroty found that 82% of verified OT intrusions used internet-facing remote access as the initial entry point. But initial access alone does not cause operational disruption. Lateral movement does. The attacker’s ability to traverse from the compromised entry point to SCADA servers, engineering workstations, historian databases, and safety systems determines whether the incident remains an IT security event or becomes an operational shutdown.
The SANS 2025 ICS/OT Security Survey confirmed that 40% of OT security incidents caused operational disruption. The question for security architects designing OT network defenses is not whether segmentation is necessary – it is which segmentation architecture actually prevents lateral movement in industrial environments.
This article compares microsegmentation vs. VLAN segmentation for OT networks across twelve evaluation dimensions, explains where each approach succeeds and fails, and provides a decision framework for selecting the right architecture based on OT maturity level and operational constraints.
How Does VLAN Segmentation Work in OT Networks?
VLAN (Virtual Local Area Network) segmentation operates at Layer 2 of the OSI model. It divides a physical network into multiple logical broadcast domains using managed switches. Each VLAN creates a separate broadcast domain – devices within the same VLAN can communicate directly, while traffic between VLANs must pass through a router or Layer 3 switch where access control lists (ACLs) can filter traffic.
In OT environments, VLAN segmentation typically follows the Purdue Model. Each Purdue level (Level 0 – physical process, Level 1 – basic control, Level 2 – area supervisory, Level 3 – site operations, Level 3.5 – IDMZ, Level 4 – enterprise) receives one or more dedicated VLANs. Inter-VLAN traffic is filtered through firewall rules or router ACLs at each boundary.
What VLAN Segmentation Does Well in OT
VLAN segmentation provides genuine value in OT environments. It reduces broadcast domain size, which improves network performance and limits the scope of broadcast storms. It provides basic isolation between Purdue levels, aligning with IEC 62443 zone requirements at a macro level. It is well understood by OT network engineers, compatible with existing managed switches, and does not require software agents on OT endpoints.
For organizations at the beginning of their OT segmentation journey – moving from a completely flat network to any level of segmentation – VLANs represent a practical, achievable first step.
Where VLAN Segmentation Fails in OT
The critical limitation of VLAN segmentation is what happens inside a VLAN. Within a single VLAN, all devices communicate freely with no access control, no traffic inspection, and no policy enforcement. If an attacker compromises one device in a VLAN containing 30 PLCs and 5 engineering workstations, the attacker can reach all 35 devices without crossing any security boundary.
CISA’s 2025 guidance stated explicitly that static zones and VLANs are no longer sufficient – segmentation must be dynamic and context-aware, factoring in identity, device posture, and behavioral signals.
The specific failures of VLAN segmentation in OT include:
No east-west traffic control. VLANs filter north-south traffic (between VLANs) but provide zero visibility or control over east-west traffic (within a VLAN). In OT environments, dozens of devices – PLCs, HMIs, RTUs, engineering workstations, historian servers – often reside in the same VLAN. Lateral movement within that VLAN is unrestricted.
Static policies. VLAN membership is based on switch port or MAC address – not on identity, device posture, or operational context. When a vendor connects a laptop to a switch port assigned to an OT VLAN, the laptop receives the same network access as the PLC on the adjacent port.
ACL sprawl. As organizations add exceptions and allow-rules to inter-VLAN ACLs, the rule sets grow unwieldy. One security architect described the result as VLANs that “look like Swiss cheese as allow-rules accumulate.” Misconfigured ACLs are a common finding in OT security assessments.
No identity awareness. VLANs do not know who is using a device or what application is generating traffic. A compromised HMI running ransomware generates traffic that is indistinguishable from legitimate HMI traffic at the VLAN level.
Reconfiguration requires physical changes. Moving a device to a different VLAN requires switch port reconfiguration or VLAN trunk changes – operations that OT teams avoid in production environments due to the risk of disrupting process control.
How Does Microsegmentation Work in OT Networks?
Microsegmentation operates at a fundamentally different level. Instead of dividing the network into broadcast domains, microsegmentation creates a security boundary around each individual endpoint or workload. Each device operates in its own security zone. Communication between devices requires explicit policy authorization – regardless of whether the devices are in the same VLAN, subnet, or physical network.
In OT environments, microsegmentation enforces policies based on identity attributes – device type, user identity, role, device posture, application, and operational context – rather than IP address or switch port. A policy might state: “Engineering Workstation EW-03 can communicate with PLC-07 on Modbus/TCP port 502, but only when accessed by a user in the OT Engineering AD group, during scheduled maintenance windows.”
Research published in the European Journal of Computer Science and Information Technology (2025) quantified the impact: microsegmentation alone achieves 87.3% lateral movement prevention, and when combined with Zero Trust principles, that figure reaches 95.8%.
Organizations exploring the fundamental differences between these approaches can find a detailed technical comparison of identity-based segmentation vs. network segmentation that covers deployment models, policy mechanics, and compliance mapping.
The Complete Comparison: Microsegmentation vs. VLAN for OT
The following table evaluates microsegmentation vs. VLAN segmentation for OT networks across twelve dimensions that matter to security architects designing industrial network defenses.
Dimension | VLAN Segmentation | Microsegmentation | Why It Matters for OT |
Segmentation granularity | Segment = group of devices (typically 10–100 per VLAN) | Segment = individual device or workload | Determines whether a single compromised device exposes the entire segment |
East-west traffic control | None within a VLAN – devices communicate freely | Full control – every device-to-device flow requires policy authorization | Most OT lateral movement occurs east-west within segments, not between them |
Policy basis | Switch port, MAC address, or VLAN tag (Layer 2) | Identity, role, device type, posture, application, time (Layer 7) | Identity-based policies survive IP changes and follow devices across locations |
Lateral movement prevention | Prevents movement between VLANs only – unrestricted within | Prevents movement between all devices – even within the same network zone | CISA 2025: VLANs alone insufficient; must enforce dynamic, context-aware controls |
OT protocol awareness | No protocol inspection – filters by IP/port only | Can enforce protocol-specific policies (Modbus, EtherNet/IP, DNP3) | OT protocols lack built-in authentication – segmentation must compensate |
Agent requirement | No agents required – enforced at switch level | Depends on implementation – agentless options available for legacy OT | Legacy PLCs and RTUs cannot run agents; agentless enforcement is required |
Policy management at scale | ACL rule count grows exponentially with device count | Policy defined by identity attributes – scales linearly with device types | A 500-device OT network may require thousands of ACL rules but only dozens of identity policies |
Impact of misconfiguration | Misconfigured ACL exposes entire VLAN to unauthorized traffic | Misconfigured policy affects only the specific device or communication path | OT misconfiguration can disrupt physical processes – blast radius matters |
Compliance alignment | Meets IEC 62443 zone requirements at macro level only | Maps directly to IEC 62443 zones, conduits, and security levels per device | Auditors increasingly require per-device policy evidence, not just network diagrams |
Deployment disruption | Requires switch reconfiguration, VLAN trunk changes, potential downtime | Software-defined – can deploy in monitor mode before enforcing | OT environments cannot tolerate unplanned downtime for security changes |
Visibility | No visibility into intra-VLAN traffic | Full visibility into all device-to-device communication flows | Visibility is prerequisite for both security and troubleshooting in OT |
Integration with identity systems | No native integration – VLAN assignment is static | Integrates with Active Directory, SAML, RADIUS for dynamic policy | Enables per-user, per-device access control tied to organizational identity |
Why VLANs Alone Cannot Prevent Lateral Movement in OT
The comparison table reveals a structural limitation that no VLAN configuration can overcome: VLANs create boundaries between groups of devices, not between individual devices. Inside a VLAN, every device trusts every other device.
Consider a typical OT Level 2 VLAN containing 8 HMI panels, 4 engineering workstations, 2 historian servers, and a patch management server. An attacker who compromises one engineering workstation through a phishing email or a compromised vendor session now has unrestricted access to all 14 other devices in the VLAN – including the HMIs that control physical processes.
The attacker does not need to cross any VLAN boundary. The attacker does not need to exploit any firewall rule. The attacker simply uses standard protocols – RDP, SMB, WMI – to move laterally within the VLAN. This is exactly the pattern Dragos documented throughout 2025: ransomware affiliates authenticated into VPN portals, then used RDP and SMB to move toward SCADA systems within flat or poorly segmented OT zones.
The severity is captured in a single question that CISA’s microsegmentation guidance poses directly to OT operators: if you choose VLAN segmentation alone, are you willing to surrender all assets in that VLAN segment to a ransomware attack when one device is compromised?
A prevention-first approach to lateral movement requires controls that operate between every device – not just between groups of devices.
When to Use VLANs, When to Use Microsegmentation, When to Use Both
The choice between microsegmentation vs. VLAN segmentation for OT is not binary. In most OT environments, the practical answer involves both – VLANs for macro-level zone separation and microsegmentation for micro-level device isolation.
Decision Framework by OT Security Maturity
OT Security Maturity | Current State | Recommended Approach | Rationale |
Level 1 – Flat network | No segmentation, all devices on single network | Deploy VLANs first to establish Purdue-level zone boundaries | VLANs provide immediate risk reduction from a flat baseline |
Level 2 – Basic zones | VLANs separate Purdue levels, but no intra-zone controls | Add microsegmentation within critical zones (Level 2, IDMZ) | Critical OT devices need per-device isolation that VLANs cannot provide |
Level 3 – Zone + conduit | VLANs with inter-zone firewall rules, IEC 62443 zone mapping | Deploy microsegmentation across all OT zones, keep VLANs for macro structure | Full east-west control, identity-based policies, compliance evidence per device |
Level 4 – Zero Trust OT | Microsegmentation with identity-based policies, continuous verification | Extend microsegmentation to IT/OT convergence points and vendor access paths | Complete lateral movement prevention across the entire IT/OT boundary |
What to Segment First
For organizations adding microsegmentation to an existing VLAN architecture, prioritize in this order:
- IDMZ (Purdue Level 3.5) – the historian relay, patch server, access gateway, and any other service that bridges IT and OT should each be isolated in its own microsegment. This is where 75% of IT-to-OT attacks cross the boundary.
- Engineering workstations (Level 3) – these are the highest-value targets in OT because they have both network access to control systems and standard IT capabilities (email, web browsing, file sharing) that make them vulnerable to IT-based attacks.
- HMI panels (Level 2) – operator stations that control physical processes should be isolated so that a compromised HMI cannot reach other HMIs or PLCs outside its defined communication path.
- Safety Instrumented Systems (Level 1) – SIS must be segmented from process control systems so that a compromise of the DCS cannot reach the safety system.
Organizations that adopt a three-layer approach to IT-to-OT connectivity address not only east-west segmentation but also north-south access control and secure file transfer between zones – the three dimensions that together provide complete OT boundary protection.
How to Implement Microsegmentation in OT Without Disrupting Production
The primary operational concern in OT microsegmentation deployment is production disruption. A misconfigured policy that blocks legitimate communication between a PLC and its HMI can halt a physical process. This concern is valid – and it is the reason why microsegmentation platforms designed for OT provide a phased deployment model with monitor-before-enforce capability.
Phase 1: Discover and Map Communication Flows (2–4 weeks)
Deploy the microsegmentation platform in observation mode. The platform passively discovers all device-to-device communication flows in the OT network – which devices communicate with which, on which ports and protocols, at what frequency, and at what volume.
This discovery phase produces a communication flow map that most OT organizations have never had. It reveals communications that should not exist (an engineering workstation communicating directly with the internet), communications that are critical but undocumented (a historian server pulling data from 40 PLCs), and redundant paths that could be eliminated.
Phase 2: Design Least-Privilege Policies (1–2 weeks)
Using the discovered communication flows, define policies that allow only the observed legitimate communications and deny everything else. Policies are defined by identity attributes – device type, function, Purdue level, user role – not by IP address.
Phase 3: Validate in Simulation Mode (2–4 weeks)
Apply policies in simulation mode (also called monitor mode or alert-only mode). The platform evaluates every communication against the proposed policies and logs what would be allowed and what would be blocked – without actually blocking anything.
Review the simulation logs for false positives – legitimate communications that the proposed policies would incorrectly block. Adjust policies before enforcement.
Phase 4: Enforce in Waves (2–4 weeks)
Enable enforcement incrementally – starting with the IDMZ, then engineering workstations, then HMI panels, then PLCs. Each wave is monitored for operational impact. If a policy blocks a legitimate communication, it can be adjusted in real time without network reconfiguration.
Phase 5: Integrate and Operationalize (ongoing)
Connect microsegmentation policy logs to the enterprise SIEM. Define processes for policy updates when new OT devices are added, when vendor access paths change, or when maintenance activities require temporary policy exceptions.
How TerraZone’s Microsegmentation Platform Addresses OT Requirements
TerraZone’s truePass platform provides microsegmentation for OT environments through an architecture specifically designed for industrial network constraints.
The platform enforces identity-based segmentation that ties access policies to device identity, user identity, and operational context – not to IP addresses or VLAN membership. Each endpoint operates in its own security zone. Communication between zones requires explicit policy authorization based on verified identity.
Key capabilities that address OT-specific requirements:
Identity-Based Firewall (IDFW) embeds firewall enforcement directly at the endpoint level. Only authenticated and authorized users can access specific OT systems. Even if credentials are stolen, the compromised identity cannot reach systems outside its authorized communication paths.
Per-endpoint isolation treats each device as its own security zone. A compromised HMI is contained – the attacker cannot pivot to other HMIs, engineering workstations, or PLCs in the same zone.
Device posture verification evaluates security posture (OS version, patch status, firewall status, running processes, geolocation) before granting access. Non-compliant devices are blocked from connecting to critical OT systems.
Agentless enforcement options address legacy OT devices that cannot run agents. Policy enforcement occurs at the network level without requiring software on PLCs, RTUs, or legacy HMIs.
Syslog and SIEM integration exports all segmentation events to enterprise SIEM platforms, providing the unified visibility across IT and OT that compliance auditors require.
For organizations ready to move beyond traditional network segmentation, TerraZone’s next-generation microsegmentation provides dynamic policy enforcement that adapts to workload changes, follows devices across network locations, and enforces Zero Trust principles at every communication path.
Compliance Mapping: VLAN vs. Microsegmentation Against OT Standards
Standard | VLAN Segmentation Compliance | Microsegmentation Compliance |
IEC 62443 – Zones and Conduits | Partially meets FR5 (Restricted Data Flow) at zone level | Fully meets FR1-FR7 with per-device policy enforcement per zone and conduit |
NIST SP 800-82 Rev 3 | Meets basic segmentation recommendation | Meets advanced recommendation for identity-based access control per OT asset |
NIST SP 800-207 (Zero Trust) | Does not align – VLANs are location-based, not identity-based | Directly aligned – policies based on identity, device, and context per request |
NERC CIP-005-7 | Meets Electronic Security Perimeter definition at zone boundary | Exceeds requirements with per-device perimeters and continuous access verification |
TSA Security Directive | Meets basic segmentation requirement | Meets advanced requirement for dynamic, context-aware segmentation |
CISA ZTMM | Scores at Traditional/Initial maturity levels | Scores at Advanced/Optimal maturity levels |
Frequently Asked Questions
What is the main difference between microsegmentation and VLAN segmentation in OT?
VLAN segmentation creates boundaries between groups of devices. Microsegmentation creates boundaries around each individual device. In an OT environment, this distinction determines whether a single compromised device exposes 10–100 other devices in the same VLAN or is contained as an isolated incident. VLANs prevent movement between zones. Microsegmentation prevents movement everywhere.
Can microsegmentation replace VLANs in OT networks?
Microsegmentation does not require removing existing VLANs. In practice, most OT environments benefit from a layered approach: VLANs provide macro-level zone separation aligned with the Purdue Model, and microsegmentation provides micro-level device isolation within those zones. The VLANs remain as the structural foundation. Microsegmentation adds the per-device access control that VLANs cannot provide.
Does microsegmentation require agents on OT devices?
Not necessarily. Modern microsegmentation platforms offer agentless enforcement options for legacy OT devices (PLCs, RTUs, legacy HMIs) that cannot support agent installation. Agent-based enforcement provides deeper visibility on devices that can support it (engineering workstations, historian servers, modern HMIs). The optimal deployment uses agents where possible and agentless enforcement where necessary.
How long does microsegmentation deployment take in OT environments?
A phased deployment – discovery, policy design, simulation, staged enforcement – typically takes 8 to 14 weeks for an OT environment with 200–500 devices. The discovery and simulation phases run passively with zero production impact. Enforcement is applied incrementally, starting with the highest-risk zones.
What is the cost difference between VLAN and microsegmentation for OT?
VLAN segmentation has lower initial cost – it requires only managed switches and router/firewall configuration. However, ACL management costs grow significantly as device counts increase (rule sets become exponentially complex). One industrial manufacturer reported avoiding $18.5 million in network infrastructure upgrades across 53 facilities by implementing software-defined microsegmentation instead of expanding the VLAN-based architecture. The total cost of ownership comparison favors microsegmentation for environments with more than approximately 100 OT devices.
Which compliance standards require microsegmentation vs. VLAN for OT?
No standard explicitly mandates microsegmentation by name. However, CISA’s 2025 guidance explicitly states that VLANs alone are insufficient and that segmentation must be dynamic and context-aware. IEC 62443 requires access control at the zone and conduit level – which microsegmentation addresses more completely than VLANs. NIST SP 800-207 requires identity-based access control – which VLANs cannot provide. Organizations targeting CISA ZTMM Advanced or Optimal maturity levels require microsegmentation.
Conclusion
The comparison between microsegmentation vs. VLAN segmentation for OT networks comes down to a single architectural question: does your segmentation prevent lateral movement between every device, or only between groups of devices?
VLANs provide valuable macro-level zone separation. They reduce broadcast domains, align with the Purdue Model, and require no endpoint agents. For organizations moving from flat networks to any level of segmentation, VLANs are the correct first step.
But VLANs cannot control east-west traffic within a zone. They cannot enforce identity-based access policies. They cannot isolate a compromised HMI from the 30 other devices in the same VLAN. When Dragos reports that ransomware affiliates use RDP and SMB to move laterally within OT zones, VLANs offer no defense against that movement.
Microsegmentation closes this gap by creating per-device security zones with identity-based policies. Research confirms a 95.8% reduction in lateral movement when microsegmentation is combined with Zero Trust principles. For OT environments where lateral movement translates to physical operational disruption, that difference is the difference between a contained security incident and a production shutdown.
The practical path forward is layered: VLANs for macro structure, microsegmentation for micro enforcement. Start with the IDMZ and engineering workstations, validate in simulation mode, enforce in waves, and extend to all OT zones. The segmentation technology exists. The implementation methodology is proven. The attacker’s playbook has not changed – lateral movement remains the critical enabler. The segmentation architecture that stops lateral movement everywhere, not just at zone boundaries, is the architecture that protects OT.