TL;DR
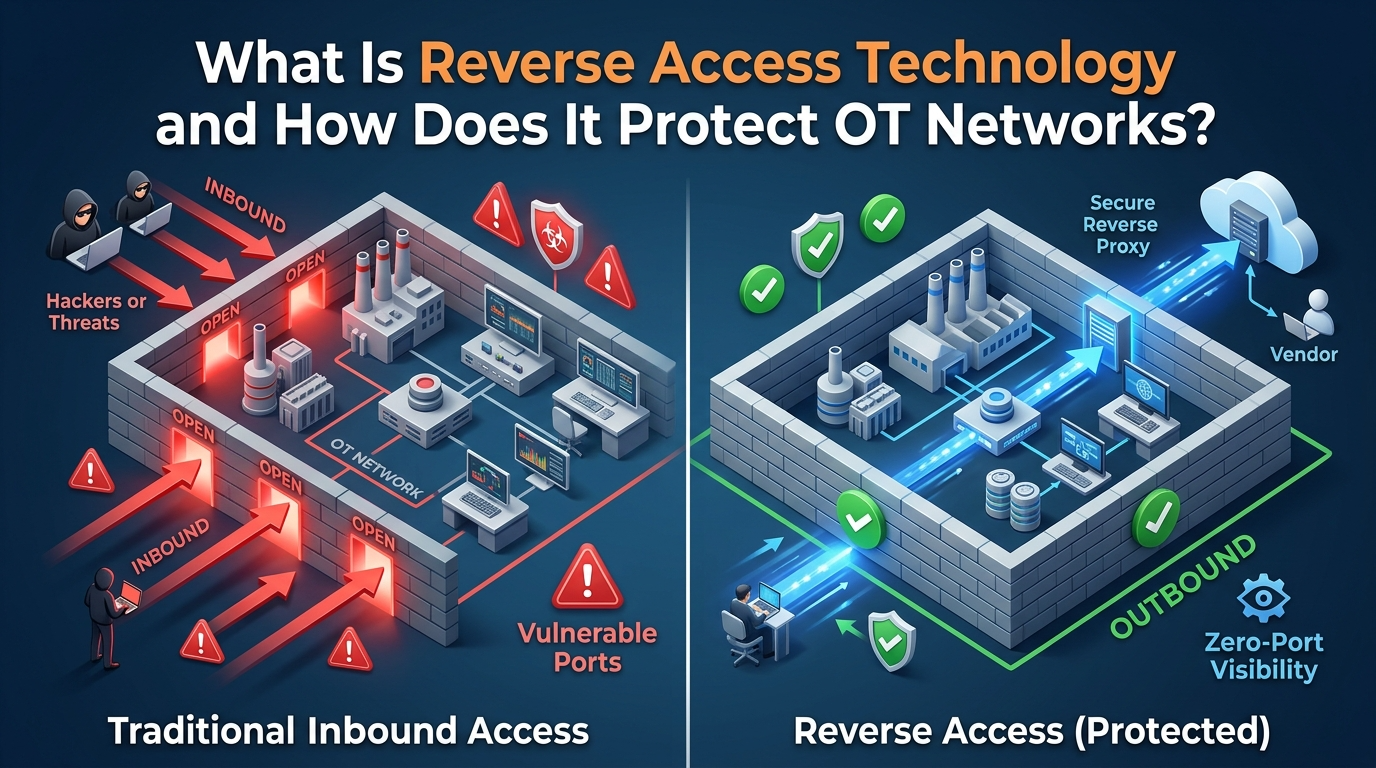
Reverse access technology is a network architecture that eliminates inbound firewall ports by inverting the connection flow: instead of external users connecting inward to OT systems, internal components initiate all connections outbound. The result is a firewall in permanent deny-all state for inbound traffic – no open ports, no listening services, no discoverable attack surface. In January 2026, a joint CISA, NCSC-UK, FBI, and Five Eyes guidance explicitly stated that all connections with OT environments should be initiated as outbound connections from within the OT environment. This principle invalidates most traditional VPN and jump server architectures and establishes reverse access as the baseline for modern OT security. With 82% of OT intrusions in 2025 exploiting internet-facing remote access tools and 65% of OT environments having insecure remote access conditions, reverse access addresses the single largest attack vector in industrial cybersecurity.
What Is Reverse Access Technology?
Reverse access technology is a connection architecture in which the protected network – the OT environment – initiates all communication outward to an external gateway or broker. External users never connect inward. The firewall does not need to open any inbound ports because no inbound connections are expected, accepted, or possible.
How It Differs from Traditional Remote Access
In a traditional OT remote access architecture, external users (engineers, vendors, operators) connect inbound through a VPN concentrator, jump server, or remote desktop gateway that sits in the Industrial DMZ (IDMZ). The firewall must open at least one inbound port (typically TCP 443, 3389, or 22) to allow these connections. This creates a listening service with a public IP address – discoverable by internet scanning tools, targetable by attackers, and subject to every vulnerability in the VPN or gateway software.
In reverse access architecture:
- A lightweight connector is deployed inside the IDMZ or the OT network boundary
- The connector initiates an outbound-only encrypted connection to an external access gateway
- The firewall permits only this outbound connection – zero inbound ports are opened
- Remote users authenticate at the external gateway
- The gateway routes authorized sessions through the existing outbound tunnel back to the specific OT application the user is permitted to access
- The OT network has no public IP address, no listening services, and no discoverable attack surface
The fundamental security property is that the firewall remains in permanent deny-all for all inbound traffic. There is nothing for an attacker to discover, probe, or exploit from outside.
Definition in Technical Terms
Reverse access is defined by three properties:
Outbound-only initiation. All TCP/TLS connections are established from the OT side outward. The OT connector opens a persistent or on-demand outbound tunnel to the access gateway. No SYN packet from the internet ever reaches the OT firewall.
No inbound listening services. The OT network exposes zero ports to the internet. There is no VPN concentrator, no RDP listener, no SSH daemon, and no web server accepting inbound connections. Internet scanning tools (Shodan, Censys, ZoomEye) return zero results for the OT network’s IP range.
Brokered access at the gateway. All authentication, authorization, and session management occur at the external gateway – outside the OT network. Only after identity verification, device posture assessment, and policy evaluation does the gateway route the session through the outbound tunnel to the specific OT resource. The user never receives network-level access to OT.
Why Reverse Access Matters Now: The 2026 Government Mandate
In January 2026, the UK National Cyber Security Centre (NCSC-UK) published Secure Connectivity Principles for Operational Technology, co-signed by CISA, FBI, Australia’s ACSC, Canada’s Cyber Centre, Germany’s BSI, the Netherlands’ NCSC-NL, and New Zealand’s NCSC-NZ. This is not vendor guidance – it is Five Eyes plus European intelligence-grade doctrine for how critical infrastructure networks should be connected.
The single most consequential statement in the guidance: “All connections with the OT environment should be initiated as outbound connections from within the OT environment.”
As security analyst Ampyx Cyber noted, this one requirement invalidates most of today’s remote access and integration patterns – VPN concentrators expecting inbound connections, jump servers with open RDP ports, vendor portals exposed to the internet. The guidance makes outbound-only connectivity the baseline architecture for OT security, not an optional enhancement.
The guidance also calls for brokered connections through secure gateways in a DMZ for all external access, just-in-time connectivity (enabled only when needed, disabled otherwise), hardware-enforced unidirectional controls for high-risk environments, and microsegmentation to limit lateral movement within OT zones.
The Threat Landscape That Demands Reverse Access
The Numbers
Threat Metric | Value | Source |
OT intrusions via internet-facing VNC (2025) | 82% | Claroty, 2026 |
OT environments with insecure remote access | 65% | Dragos OT Report, 2025 |
OT attacks originating as IT breaches crossing into OT | 75% | Industry data, 2025 |
SSH exposed to publicly routable addresses in OT orgs | 45% | Dragos, 2025 |
YoY increase in ransomware groups targeting OT | 60% | Dragos, 2025 |
YoY ransomware spike in manufacturing | 87% | Dragos, 2025 |
OT attack detections in manufacturing sector | 42% | Trellix, 2025 |
Average OT vulnerability patching time | 180 days | Trellix, 2025 |
Daily IoT/OT hacking attempts globally | 820,000 | DeepStrike, 2025 |
Hacktivist sightings increase (2024→2025) | 51% | Cyble, 2026 |
ICS vulnerabilities disclosed (Dec 2024–Nov 2025) | 2,451 | Cyble, 2026 |
Dual IT/OT attack average cost | $4.56 million | Industry data, 2026 |
How Attacks Exploit Inbound Ports
The pattern is consistent across nearly every major OT breach:
Step 1: Discovery. Attackers scan the internet for exposed OT services. VPN concentrators, RDP jump servers, VNC endpoints, and SCADA web interfaces are indexed by tools like Shodan. In 2025, Claroty found that attackers used freely available tools – UltraVNC, TightVNC, Metasploit, modbus-cli – to identify and exploit these exposed services.
Step 2: Credential compromise. Attackers obtain credentials through phishing, credential stuffing, or purchasing stolen credentials from Initial Access Brokers on dark web marketplaces. In 2025, compromised credentials were the most common root cause of OT ransomware attacks (Sophos). 44% of financial services respondents cited “unknown security gaps” as the entry point.
Step 3: Inbound connection. The attacker connects through the open inbound port using stolen credentials. The VPN or jump server authenticates the session as legitimate. The attacker is now inside the OT network with whatever level of access the compromised account permits.
Step 4: Lateral movement. Once inside, the attacker moves laterally – from the VPN landing zone to SCADA servers, HMI stations, PLCs, and historians. The Dragos 2025 report found that living-off-the-land techniques (using built-in tools to avoid detection) are increasingly popular in OT environments, making lateral movement harder to detect.
Step 5: Impact. The attacker achieves their objective – ransomware deployment, data exfiltration, operational disruption, or physical damage to industrial processes.
Reverse access breaks this chain at Step 1. If there is no inbound port, there is nothing to discover. If there is nothing to discover, there is nothing to connect to. The entire attack sequence – from reconnaissance to impact – depends on the existence of an internet-facing service. Reverse access eliminates it.
How Reverse Access Architecture Works: Technical Deep Dive
Connection Lifecycle
Phase 1: Connector Initialization
The OT-side connector establishes an outbound TLS 1.3 connection to the access gateway. This connection is initiated from inside the OT network – the firewall sees it as an outbound session and permits it under standard egress rules. The connector authenticates to the gateway using mutual TLS (mTLS) with certificate-based identity. The tunnel remains persistent (keep-alive) or is established on-demand depending on the deployment model.
Phase 2: User Authentication
A remote user (engineer, vendor, operator) navigates to the access gateway and authenticates. Authentication includes identity verification against the organization’s IdP (Active Directory, Okta, Entra ID), multi-factor authentication (FIDO2 hardware key, authenticator app, or SMS), device posture assessment (OS version, EDR status, disk encryption, compliance), and contextual evaluation (location, time, network type, behavioral patterns).
Phase 3: Policy Evaluation
The gateway’s policy engine evaluates the authenticated user’s request against the access policy: which OT application is the user authorized to access? Under what conditions (time window, device posture, location)? With what permissions (view-only, interactive, administrative)? Is session recording required? Is the session time-bounded?
Phase 4: Session Establishment
If the policy permits access, the gateway routes the user’s session through the existing outbound tunnel to the specific OT application. The user receives application-level access – not network-level access. They can interact with the specific SCADA HMI, PLC programming interface, or historian dashboard authorized by policy. They cannot scan the network, access other devices, or move laterally.
Phase 5: Continuous Monitoring and Termination
Throughout the session, the gateway monitors for anomalous behavior, device posture changes, and policy violations. If the user’s device becomes non-compliant, or if the session exceeds its time limit, or if anomalous activity is detected, the session is terminated automatically. Every action is logged in an immutable audit trail.
What the Firewall Looks Like
Firewall Rule | Traditional OT Access | Reverse Access |
Inbound from Internet | ALLOW TCP 443 to VPN (source: any) | DENY ALL (no exceptions) |
Inbound from IT zone | ALLOW TCP 3389 to jump server | DENY ALL (no exceptions) |
Outbound to gateway | N/A | ALLOW TCP 443 from connector to gateway IP |
Default inbound policy | Allow specific, deny rest | Deny all – permanently |
Shodan/Censys visibility | VPN, RDP, or VNC detected | Nothing detected |
Reverse Access vs. Alternative OT Security Architectures
vs. Traditional VPN
Dimension | VPN | Reverse Access |
Inbound ports required | Yes (at least 1) | None |
Network-level access after auth | Yes – full zone access | No – application-level only |
Attack surface | VPN concentrator is internet-facing | Zero – nothing is internet-facing |
Credential brute-force exposure | VPN login page is public | Authentication at gateway, OT is invisible |
Lateral movement after compromise | Attacker has network access | Attacker has access to 1 application only |
IEC 62443 conduit compliance | Opens conduit from internet to OT | Conduit initiated from OT outward |
CISA/NCSC 2026 alignment | Does not meet outbound-only principle | Fully aligned |
vs. Jump Server / Bastion Host
Jump servers concentrate all remote access through a single hardened system in the IDMZ. They require inbound connectivity (RDP or SSH) to the jump server, a persistent server that must be patched, monitored, and maintained, and manual administration to open and close access windows. Jump servers reduce the attack surface compared to direct VPN, but they do not eliminate it – the jump server itself is an internet-facing target. Claroty’s 2025 analysis found that jump servers suffer from the same vulnerability exposure as VPNs because they require open ports and are rarely patched at the cadence required for internet-facing systems (180-day average OT patching cycle).
vs. Hardware Data Diodes
Unidirectional security gateways (data diodes) physically enforce one-way data flow. They are the strongest possible control for data exfiltration prevention. However, hardware diodes enforce unidirectional data flow – they cannot support bidirectional remote access sessions (viewing an HMI, programming a PLC, troubleshooting SCADA). Reverse access architecture supports full bidirectional sessions while maintaining the outbound-only connection initiation principle. For environments requiring both data export and remote access, reverse access and data diodes serve complementary roles: data diodes for unidirectional historian replication, and reverse access for interactive remote sessions.
vs. Cloud-Native ZTNA
Cloud ZTNA solutions (Zscaler, Cloudflare, Palo Alto Prisma) use service-initiated connectors that establish outbound connections to the vendor’s cloud. This is architecturally similar to reverse access – no inbound ports are required on the OT side. However, cloud ZTNA routes all session traffic through the vendor’s cloud infrastructure. For OT environments subject to data sovereignty requirements, air-gap mandates, or classified-network restrictions, cloud ZTNA may be disqualifying. On-premises reverse access deployments keep all traffic within the organization’s infrastructure – the access gateway runs in the organization’s DMZ or private cloud, not in a third-party environment.
IEC 62443 Compliance: How Reverse Access Meets Every Foundational Requirement
IEC 62443 FR | Requirement | How Reverse Access Addresses It |
FR1 – Identification & Authentication | Verify all users before access | Users authenticate at the gateway with MFA + device posture before any OT connection |
FR2 – Use Control | Enforce permissions of authenticated users | Per-application, per-user policies with time-bounded sessions and least privilege |
FR3 – System Integrity | Prevent unauthorized modification | No inbound traffic reaches OT. Session recording captures all actions for integrity verification |
FR4 – Data Confidentiality | Encrypt communications | All sessions encrypted end-to-end (TLS 1.3 / AES-256) |
FR5 – Restricted Data Flow | Control data movement between zones | Only explicitly defined outbound conduits exist. Microsegmentation isolates tiers |
FR6 – Timely Response | Log and respond to events | Immutable audit trails per session. SIEM integration for real-time alerting |
FR7 – Resource Availability | Maintain system availability | No DDoS target exists. OT availability is not threatened by external traffic |
Security Level Alignment
IEC 62443 SL | What It Protects Against | VPN Architecture | Reverse Access |
SL1 | Casual/accidental violation | Meets with basic MFA | Exceeds – no ports to probe |
SL2 | Simple intentional attack | Requires hardened VPN + segmentation | Meets natively |
SL3 | Sophisticated intentional attack | Fails – VPN is exploitable | Meets – no inbound conduit |
SL4 | State-sponsored attack | Fails – any internet-facing service is vulnerable | Approaches – infrastructure invisible |
Who Needs Reverse Access Technology?
By Industry
Manufacturing – 42% of all OT attack detections. Legacy PLCs and HMIs cannot be patched fast enough to survive internet exposure. Reverse access eliminates the exposure entirely.
Water and Wastewater – Disproportionately targeted by hacktivists (Z-Pentest, Dark Engine, Sector 16) and nation-state actors. Small utilities with limited security staff need architecture that defends itself, not architecture that requires active threat management.
Energy and Utilities – Nation-state campaigns (ELECTRUM, Sandworm, Volt Typhoon, Salt Typhoon) specifically target energy infrastructure. IEC 62443 SL3/SL4 requirements for energy demand the strictest conduit controls.
Oil and Gas – Pipeline SCADA, refinery DCS, and offshore platform operations depend on remote access across geographically dispersed sites. The Colonial Pipeline attack demonstrated the consequences.
Transportation – Ranked as the most targeted OT sector in H1 2025 (Nozomi Networks). Traffic control, rail signaling, port operations, and airport infrastructure all require remote vendor and engineering access.
Healthcare – IoMT (Internet of Medical Things) shares OT characteristics: legacy OS, proprietary protocols, devices that cannot be patched during operation. Average IoMT breach cost: $10 million.
Government and Defense – Classified networks require zero inbound exposure by policy. On-premises deployment with identity isolation ensures that no traffic traverses external infrastructure.
By Role
OT Security Managers need architecture that closes the remote access vulnerability without disrupting plant operations. Reverse access achieves this by changing only the connection direction, not the end-user workflow.
Plant/Operations Managers need assurance that remote access will not introduce downtime risk. Reverse access eliminates the most common disruption vector (DDoS and exploitation of internet-facing VPN/jump servers) while maintaining the remote access capability operations depend on.
CISOs need defensible architecture that satisfies regulatory examination. Reverse access maps directly to CISA/NCSC 2026 guidance, IEC 62443, and NIST SP 800-82 – providing clear audit evidence of compliant OT connectivity.
Compliance Officers need documented evidence that OT access controls meet framework requirements. Reverse access generates complete, per-session audit trails with user identity, device posture, application accessed, actions performed, and session duration – satisfying NERC CIP, IEC 62443, NIST CSF, and sector-specific mandates.
Real-World Scenario: Before and After
Power Utility – Remote SCADA Access
Before (Traditional VPN):
- Cisco AnyConnect VPN with TCP 443 open to SCADA IDMZ
- 12 vendor accounts sharing 3 VPN credentials
- VPN grants network-level access to entire SCADA zone
- Jump server in IDMZ with RDP port 3389 open
- No session recording. No time-bounded access
- Shodan scan: 2 services detected (VPN, RDP)
- Last VPN firmware update: 9 months ago
After (Reverse Access):
- Outbound-only connector in IDMZ → access gateway
- 12 individual vendor accounts with MFA and device posture verification
- Each vendor receives access to their specific equipment only – no network access
- All sessions recorded with keystroke logging
- Time-bounded access: 4-hour windows with automatic expiration
- Shodan scan: 0 services detected
- Firewall: deny-all inbound – no exceptions
Implementation Checklist
Assessment
- [ ] Inventory every inbound firewall rule to OT (port, protocol, source, purpose)
- [ ] Document all remote access tools (VPN, RDP, VNC, TeamViewer, vendor portals)
- [ ] Map all data flows crossing IT/OT boundary
- [ ] Identify all external users accessing OT (vendors, contractors, remote engineers)
- [ ] Classify each access by Purdue level, application, protocol, and frequency
Architecture
- [ ] Deploy reverse-access connector in IDMZ
- [ ] Configure outbound-only TLS connection to access gateway
- [ ] Set firewall to deny-all inbound – no exceptions
- [ ] Define per-user, per-application access policies
- [ ] Configure time-bounded vendor sessions with auto-expiration
- [ ] Enable session recording for all OT sessions
- [ ] Implement MFA (FIDO2 or hardware tokens)
- [ ] Deploy identity-based segmentation within OT zones
Validation
- [ ] External scan (Shodan, Censys, Nmap) – verify zero results
- [ ] Penetration test targeting OT remote access paths
- [ ] Verify firewall deny-all with stateful inspection
- [ ] Test vendor workflow: auth → access → recording → expiration
- [ ] Validate audit trail against IEC 62443 FR6
- [ ] Document architecture for compliance examination
Frequently Asked Questions
What is the difference between reverse access and a data diode?
A data diode enforces physically unidirectional data flow – data can move in one direction only (typically from OT outward). It cannot support interactive remote access sessions. Reverse access supports bidirectional sessions (viewing HMIs, programming PLCs) while maintaining outbound-only connection initiation. They serve complementary purposes: data diodes for unidirectional data export, reverse access for interactive remote sessions.
Does reverse access introduce latency to OT operations?
The outbound tunnel adds minimal latency – typically single-digit milliseconds. For HMI viewing and PLC programming, this is imperceptible. For real-time control loops, reverse access is used for engineering and maintenance access, not for the control loop itself (which operates locally within the OT network).
Can reverse access support legacy OT protocols (Modbus, DNP3)?
Yes. The connector tunnels traffic at the network layer, supporting any TCP-based protocol. The remote user’s session is encapsulated within the outbound TLS tunnel regardless of the application protocol used inside it. This includes Modbus/TCP, DNP3, OPC-UA, proprietary PLC programming protocols, and even SMB file sharing.
What happens if the outbound connection drops?
If the outbound tunnel is disrupted, all remote sessions are terminated. The OT network returns to its default state: fully isolated with no external connectivity. This is a fail-closed design – disruption to the remote access path cannot create an opening in the firewall.
Is reverse access required by regulation?
The CISA/NCSC-UK 2026 Secure Connectivity Principles for OT guidance states that all OT connections should be outbound-initiated. While framed as goals rather than mandatory requirements, the guidance represents the consensus position of Five Eyes plus European intelligence agencies. IEC 62443 does not explicitly mandate reverse access, but its zone-and-conduit model and SL3/SL4 requirements are most effectively met by eliminating inbound conduits – which reverse access achieves by design.
How does reverse access compare to ZTNA?
Reverse access is a network architecture pattern. ZTNA (Zero Trust Network Access) is a broader security framework. The best ZTNA solutions for OT use reverse access as their underlying connection architecture – providing the zero-inbound-port property while adding identity verification, device posture assessment, policy enforcement, and session management on top.
Conclusion
Reverse access technology is the architectural answer to the single largest vulnerability in OT security: internet-facing remote access. By inverting the connection flow – OT initiates outbound, users connect at the gateway – the firewall stays in permanent deny-all for inbound traffic. No open ports. No discoverable services. No attack surface.
The January 2026 CISA/NCSC-UK joint guidance made this architecture the international baseline for OT connectivity. The 2025 threat data – 82% of intrusions via internet-facing tools, 65% insecure remote access, 87% ransomware surge in manufacturing – demonstrates why the baseline is necessary.
For OT security managers, plant operators, and CISOs, the question is no longer whether to adopt outbound-only connectivity. The question is how quickly existing inbound ports can be closed, existing VPN and jump server architectures can be replaced, and existing vendor access can be migrated to a reverse-access model that satisfies both operational requirements and the regulatory expectation that now exists.
Every inbound port that remains open is a conscious decision to accept a risk that every major cybersecurity authority in the Western world has said is no longer acceptable.