The Math That Proves Detection Is Losing
There is a fundamental arithmetic problem at the center of enterprise cybersecurity, and most organizations are on the wrong side of it.
In 2026, the average time for an attacker to move laterally from an initial compromised endpoint to the next system is 34 minutes. The fastest observed lateral movement took just 4 minutes, an 85% drop from the previous year. CrowdStrike reports eCrime breakout time – from initial access to lateral movement – averaging 48 minutes, with the fastest attack recorded at 51 seconds. Palo Alto Networks found that in 20% of cases, data was stolen in under an hour.
On the other side: the average organization takes two full weeks to respond to and contain a security alert. Ransomware actors had access to systems for an average of two weeks before a ransomware incident was triggered. The median dwell time – how long an attacker remains undetected – stands at 11 days according to Mandiant, though sophisticated attackers operating with living-off-the-land techniques remain undetected for months or years.
The gap between attacker speed and defender response is not closing. It is widening. In 2026, lateral movement times dropped 29% year-over-year. Data exfiltration accelerated from four hours to six minutes. Every incremental improvement in detection speed is outpaced by a larger acceleration in attack speed.
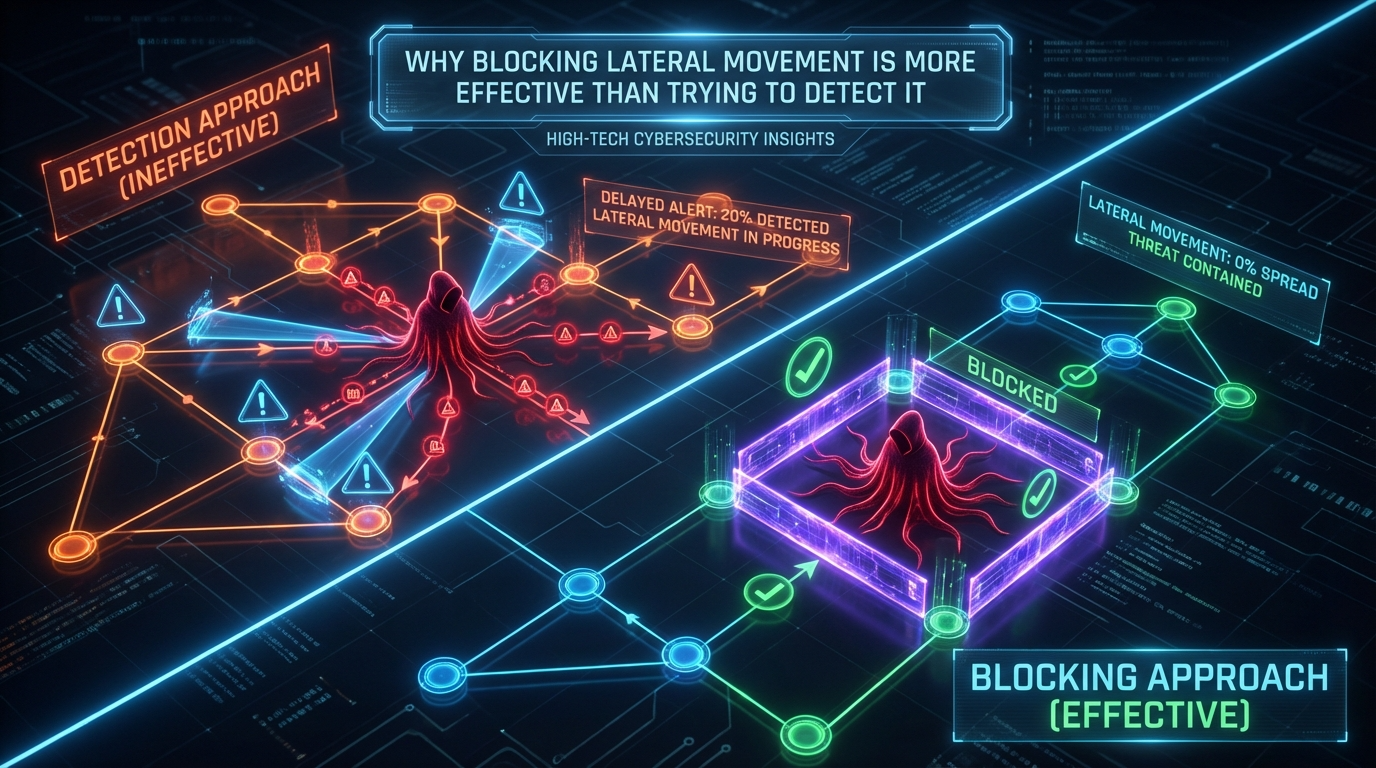
This article makes the case – with data, architecture analysis, and operational reality – that attempting to detect lateral movement after it starts is a losing strategy. Prevention-first architectures that block lateral movement before it begins are fundamentally more effective, more reliable, and more cost-efficient than detection-and-response approaches that race against an attacker who is already inside.
Why Detection-First Architectures Fail Against Lateral Movement
Detection tools – EDR, NDR, SIEM, XDR – are designed to identify suspicious activity after it occurs. They analyze logs, correlate events, flag anomalies, and alert analysts. For many threat categories, this model works. For lateral movement, it fails systematically. Here is why.
Attackers Use Legitimate Tools
Living-off-the-land (LOTL) techniques now fuel 84% of severe breaches. Attackers use PowerShell, WMI, PsExec, RDP, and other built-in administrative tools to move between systems. These are the same tools that IT administrators use every day. CrowdStrike reports that 79% of observed detections in 2026 were malware-free – relying entirely on hands-on-keyboard techniques and native system binaries.
When an attacker uses stolen domain admin credentials to connect via RDP from one server to another, the traffic looks identical to a legitimate administrator performing routine maintenance. The network signature is the same. The authentication event is valid. The protocol is standard. Detection tools must distinguish malicious RDP from legitimate RDP based on behavioral context – and that distinction is fragile, delayed, and error-prone.
The Alert Fatigue Problem
Even when detection tools do flag suspicious lateral movement, the signal is buried in noise. Security teams are overwhelmed with alerts. The average SOC processes thousands of alerts daily, and false positive rates for internal network activity – where legitimate and malicious behavior look identical – are exceptionally high. An analyst who receives an alert about an unusual RDP session must determine whether it is a sysadmin working late or an attacker pivoting to a domain controller. That determination takes minutes to hours. The attacker needs seconds.
Structural Detection Delay
Detection architectures introduce structural delay at every stage. Events are generated, collected, forwarded to a SIEM or XDR platform, ingested, indexed, correlated, scored, and then surfaced as alerts. Each stage adds latency. Even “real-time” detection typically operates on a cycle measured in minutes – the time between event generation and analyst notification.
When the attacker moves laterally in 34 minutes and exfiltrates data in 6 minutes, a detection pipeline that takes 10-15 minutes to generate an actionable alert is already too late. The attacker has moved, escalated, and potentially completed their objective before the alert reaches a human.
Detection Cannot Undo Damage
Detection tells you what happened. It does not prevent what happened from happening. When an alert fires that an attacker has moved from Workstation A to Server B, Server B is already compromised. The data on Server B is already accessible. The credentials on Server B are already harvested. Detection provides notification – not protection.
Organizations relying on detection-first approaches for lateral movement are essentially building a security architecture that says: “We will allow the attacker to move freely, and we will try to notice quickly enough to limit the damage.” The data shows that “quickly enough” is no longer achievable at human speed.
The Speed Gap: Attackers vs. Defenders in 2026
Phase | Attacker Speed (2026) | Defender Response (2026) | Gap |
Initial access to lateral movement | 34 minutes average; 4 minutes fastest | Detection pipeline: 10-30 minutes to alert | Attacker moves before alert fires |
Lateral movement to domain admin | Minutes to hours (pass-the-hash, Kerberoasting) | Investigation: hours to days | Attacker has admin before investigation begins |
Lateral movement to data exfiltration | 6 minutes fastest | Containment: 2 weeks average | Data exfiltrated before containment starts |
Full ransomware encryption | 18 minutes (LockBit 4.0 with AI) | Incident response mobilization: hours | Encryption complete before IR team assembles |
Breakout time (eCrime average) | 48 minutes (CrowdStrike 2024); 29 minutes (CrowdStrike 2026 report) | Alert triage + escalation: 30-60 minutes | Attacker breaks out during triage |
Dwell time (sophisticated APT) | Weeks to months undetected | External discovery in 43% of cases | Attacker operates freely for extended periods |
The conclusion from this data is unambiguous: detection cannot close the speed gap. When attackers complete their lateral movement in under an hour – and in many cases under 10 minutes – a detection-and-response architecture that operates on a multi-hour or multi-day cycle is structurally incapable of preventing the damage.
How Prevention-First Architecture Eliminates the Speed Gap
Prevention-first architecture does not race against the attacker. It removes the race entirely by blocking lateral movement before it starts – regardless of how fast the attacker is.
The Principle: Block Before Connect
In a prevention-first architecture, no endpoint can communicate with another endpoint unless an explicit policy permits the connection. There is no default connectivity. There is no implicit trust. Every connection request is evaluated against the segmentation policy before the first packet reaches the destination.
This means that when an attacker compromises Workstation A and attempts to connect to Server B, the connection is blocked by the segmentation policy – not because the system detected the attempt as malicious, but because Workstation A is not authorized to communicate with Server B. The attacker’s speed is irrelevant. Whether they attempt the connection in 34 minutes or 34 milliseconds, the result is the same: denied.
The Mechanism: Identity-Based Microsegmentation
Microsegmentation enforces per-endpoint access policies based on identity – not IP address, not VLAN membership, not network location. Each endpoint operates in its own security zone. Communication between zones requires explicit authorization based on verified identity and device posture.
This architecture eliminates lateral movement as a viable attack technique because the attacker cannot reach systems they are not authorized to access – even with valid credentials. A stolen admin credential that authenticates successfully is still blocked from reaching systems outside the policy-defined communication paths for that identity.
Organizations implementing SASE architectures combine this microsegmentation enforcement with secure access controls at the network edge, ensuring that prevention policies apply consistently whether users and workloads are on-premises, in the cloud, or at remote locations.
Prevention vs. Detection: The Architectural Difference
Characteristic | Detection-First (EDR/NDR/XDR) | Prevention-First (Microsegmentation) |
When it acts | After the connection is made | Before the connection is made |
What it evaluates | Behavioral patterns, anomalies, signatures | Policy authorization: is this connection permitted? |
Speed dependency | Must be faster than the attacker | Speed-independent: block is instantaneous |
False positive risk | High (legitimate and malicious traffic look similar) | Low (policy is binary: permitted or denied) |
Effectiveness against LOTL | Limited (attackers use legitimate tools) | Full (tools are irrelevant; unauthorized paths are blocked) |
Effectiveness with stolen credentials | Limited (valid credential = valid-looking activity) | Effective (credential does not override segmentation policy) |
Scalability | More endpoints = more alerts = more analyst burden | More endpoints = more policies, but enforcement is automated |
Result when triggered | Alert → investigation → response | Block → log → no lateral movement occurs |
Residual risk | Attacker may complete objective before response | Attacker is contained at point of compromise |
The 5 Lateral Movement Techniques That Detection Consistently Misses
These five techniques exploit the structural weaknesses of detection-based approaches. Each is effectively neutralized by prevention-first microsegmentation.
1. Pass-the-Hash / Pass-the-Ticket
The attacker captures a password hash or Kerberos ticket from memory on a compromised endpoint, then uses it to authenticate to other systems. The authentication is technically valid – it uses a real credential. Detection systems see a successful authentication event, not a malicious one. The attack is invisible at the network level and often at the endpoint level.
Why detection fails: The authentication event is indistinguishable from legitimate use. The credential is real. The protocol is standard.
Why prevention succeeds: Microsegmentation does not evaluate whether the credential is legitimate. It evaluates whether the connection from that endpoint to that destination is permitted by policy. If the compromised endpoint is not authorized to reach the target server, the connection is blocked – regardless of the credential’s validity.
2. RDP Lateral Movement
The attacker uses stolen credentials to establish an RDP session from one compromised system to another. RDP is the most common lateral movement protocol in enterprise environments.
Why detection fails: RDP sessions between servers or between admin workstations and servers are routine. Distinguishing malicious RDP from legitimate RDP requires behavioral analysis that is inherently delayed and unreliable.
Why prevention succeeds: In a microsegmented environment, RDP connections are permitted only between explicitly authorized source-destination pairs. A compromised workstation that is not policy-authorized to RDP into the domain controller is blocked immediately. Organizations that enforce privileged access management controls alongside microsegmentation ensure that even privileged protocols like RDP are restricted to authorized administrator-to-server pairs with just-in-time session controls.
3. SMB/CIFS File Share Exploitation
Ransomware propagates primarily through SMB file shares. Once an endpoint is encrypted, the ransomware uses the SMB protocol to reach every accessible file share on the network and encrypt them as well. On a flat network, this means every shared drive is encrypted within minutes.
Why detection fails: SMB is the most common protocol on enterprise networks. File access events are generated at enormous volume. Distinguishing ransomware encryption from legitimate file operations requires behavioral analysis that typically identifies the attack only after significant encryption has already occurred.
Why prevention succeeds: Microsegmentation restricts SMB communication to explicitly authorized paths. An endpoint in the marketing department cannot reach engineering file shares. A user workstation cannot access server-to-server SMB paths. The ransomware’s propagation is contained to the single endpoint’s authorized file shares – not the entire organization.
4. PowerShell Remoting (WinRM)
Attackers exploit PowerShell remoting to execute commands on remote systems using legitimate administrative channels. PowerShell appears in 71% of LOTL attack cases.
Why detection fails: PowerShell is a legitimate administration tool used by every IT team. Commands executed via PowerShell remoting look identical to routine automation scripts. Detecting malicious PowerShell requires deep content inspection of encrypted traffic – a capability most detection platforms lack.
Why prevention succeeds: Microsegmentation blocks WinRM connections (port 5985/5986) between endpoints that are not policy-authorized for remote administration. The attacker cannot invoke PowerShell on a remote system if the network path between the compromised endpoint and the target is blocked by segmentation policy.
5. Service Account Exploitation
Attackers compromise service accounts that have broad network access – often accounts used for backup, monitoring, or application integration. These accounts typically have persistent access to dozens or hundreds of systems.
Why detection fails: Service accounts generate enormous volumes of legitimate traffic. Authentication events for service accounts occur continuously. Identifying anomalous service account behavior requires a behavioral baseline that most organizations have never established.
Why prevention succeeds: Microsegmentation restricts service account communication to the specific servers and ports required for their function – even if the credential itself has broader Active Directory permissions. The segmentation policy overrides the AD permissions, limiting the blast radius of a compromised service account to its authorized communication paths.
The Hybrid Model: Prevention as the Foundation, Detection as the Complement
This article does not argue that detection has no value. It argues that detection is insufficient as a primary defense against lateral movement, and that prevention must be the foundation.
The optimal architecture is a hybrid model where microsegmentation prevents lateral movement by default, and detection tools provide visibility into the attempts that are blocked. The segmentation policy denies the connection. The detection tool logs the denied attempt and correlates it with other indicators. The security analyst receives an alert that an endpoint attempted an unauthorized connection – not that an endpoint successfully moved laterally and must now be investigated.
In this model, detection works as it should: identifying indicators of compromise on endpoints that have already been contained by segmentation. The analyst investigates a contained threat – not an active, spreading breach.
Prevention without detection = strong containment, limited visibility into attacker behavior. Detection without prevention = extensive visibility, limited containment, race against the clock. Prevention + detection = strong containment AND visibility, analyst investigates from a position of control.
Organizations implementing secure remote access alongside microsegmentation extend this hybrid model to remote and distributed environments, ensuring that the prevention-first architecture applies consistently regardless of user location.
The Cost Argument: Prevention Is Cheaper Than Response
The financial case for prevention over detection is straightforward.
Detection-first cost structure: SIEM licensing ($200K-$500K/year for enterprise), NDR platform ($150K-$400K/year), SOC analyst staff (3-5 analysts × $120K-$180K), incident response retainer ($100K-$300K/year), plus the full cost of breaches that detection fails to prevent in time.
Prevention-first cost structure: Microsegmentation platform ($500K-$800K initial + $150K-$250K/year), reduced SOC analyst burden (segmentation generates cleaner, lower-volume alerts), reduced IR cost (incidents are contained before investigation begins), plus insurance premium reductions (15-30%) and compliance scope reduction.
IBM’s 2026 data shows that organizations with Zero Trust controls – including microsegmentation – experienced breach costs of $4.15 million vs. $5.10 million without them. The $950K per-incident savings exceeds the annual cost of a microsegmentation platform. And that calculation assumes a breach occurs. For breach-free years, the prevention investment still delivers ROI through insurance and compliance savings.
The operational cost comparison is equally compelling. Investigating a contained incident – where the attacker was blocked at the first hop – takes hours. Investigating an uncontained breach – where the attacker moved through 50 systems over two weeks – takes weeks and costs millions.
What “Prevention-First” Looks Like in Practice
A prevention-first architecture for lateral movement requires four components:
- Default-deny network posture. No endpoint communicates with any other endpoint unless an explicit policy permits it. This is the foundation. Every connection that is not specifically authorized is blocked.
- Identity-based segmentation policies. Policies are defined by user identity, device identity, workload identity, and device posture – not by IP address or VLAN. When a user moves between networks, the policy follows them. When a VDI session is provisioned, the segmentation policy is applied based on the user’s identity and role, not the desktop’s network location.
- Continuous device compliance enforcement. Every device is evaluated continuously – not just at login. Firewall status, OS patch level, disk encryption, and endpoint agent health are checked before and during every connection. A device that becomes non-compliant is blocked from establishing new connections until remediated.
- Segmentation logging for detection enrichment. Every blocked connection is logged with source, destination, port, protocol, timestamp, and identity. These logs feed into detection tools – providing high-quality, low-noise indicators of attempted lateral movement that detection platforms can correlate without the false positive burden of analyzing all successful connections.
The Shift Security Teams Must Make
The cybersecurity industry has spent two decades building faster, smarter detection. The result: detection is better than ever – and attackers are still faster. Dwell time has decreased from 416 days to 11 days over 15 years. In the same period, attacker breakout time has decreased from hours to minutes. The gap has not closed. It has inverted.
The shift required is not incremental. It is architectural. It is the difference between building a faster alarm system and building walls that prevent entry regardless of how fast the intruder moves.
Prevention-first architecture – built on microsegmentation with default-deny policies, identity-based access controls, and continuous compliance enforcement – does not compete with attacker speed. It renders attacker speed irrelevant by eliminating the communication paths that lateral movement requires.
Detection remains essential for visibility, forensics, and investigation. But it cannot be the primary defense against an attack technique that completes faster than any detection pipeline can process. The organizations that understand this – and architect accordingly – are the ones that survive the breach without losing the network.